Linux Unix Training Classes in Little Rock, Arkansas
Learn Linux Unix in Little Rock, Arkansas and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Linux Unix related training offerings in Little Rock, Arkansas: Linux Unix Training
Linux Unix Training Catalog
subcategories
DevOps Classes
Foundations of Web Design & Web Authoring Classes
Java Programming Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
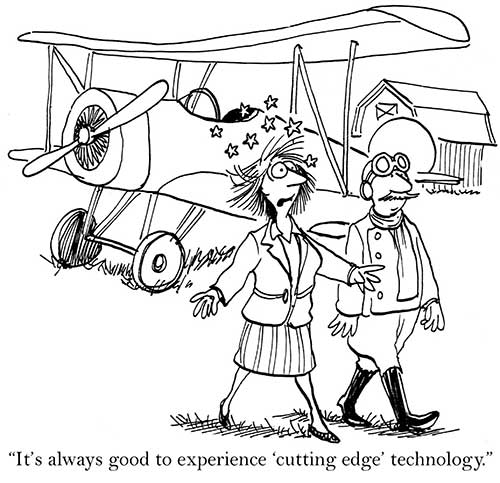
Planning on a little spring cleaning and getting rid of all those old electronics? With the way technology changes so quickly, it seems like we no sooner have one new electronic piece and there’s a new one on the market that we absolutely have to have. The result is a ton of used electronics stored away. Now it’s time to get rid of everything, here are some tips on what to do with all that old tech stuff and how to do it safely.
Save on Landfill Waste
Few people really realize where their electronics wind up when they throw them in the trash or dumpster. They assume they’re getting taken care of and just forget about them. According to the Environmental Protection Agency, one of the fastest growing components of landfill waste is electronics. The unfortunate part of this is that these electronics are filled with lead, mercury and other toxic chemicals – chemicals that find their way into our soil and water.
This results in the contamination of our lakes, streams and soil. The best way to avoid this is by knowing where your electronics are going and to dispose of them safely. Contact the recycling center in your area and ask for the best place to dispose of your old electronics.
Think of Security
Our lives are filled with electronic technology, whether it’s in the form of computers, tablets, smart phones or video games. Most of these electronics allow network sharing with people all over the world. With identity theft such a growing concern, much of our private lives and personal information is entered in the hard drives of these items.
Before you dispose of any electronics, make sure the hard drives are wiped clean of all personal information. This requires more than just “deleting” files. If you’re not sure how to correctly get rid of the information, contact a professional to do this for you. Even if you have to pay to have it done, it’s a minimal expense compared to having your private information stolen.
Find New Homes for Your Electronics
Once you’ve cleaned out your electronics of personal information, they may still be worth something to other individuals. You may know of a child or elderly person who would really appreciate a “new” computer or a tablet. Someone who has never owned a smart phone or laptop may be thrilled to suddenly own one, even if they are obsolete to you.
If you can’t find anyone that wants them, consider selling them on places like eBay, Craigslist or one of the many other online auction sites. The old saying, “one man’s junk is another man’s gold” is especially true when it comes to electronics. Many people like building computers using their own parts.
Students in computer-related programs also utilize used electronics as a form of hands-on training. Most schools also take in donated computers, televisions and cell phones. Contact your electric company or school district to get information on where you can take your old electronics. You’ll be not only cleaning out your house but also helping the environment.
Related:
Cloud Computing: What It Means and How It Could Threaten the Traditional Outsourcing Model
Microsoft has now come up with a surface tablet to compete with the Apple iPad. The Surface is the known as the ‘iPad killer’ and ‘Microsoft iPad’. Microsoft has stuck to production of software till date but this is one of its latest hardware devices that is expected to take over the Apple iPad. This is a new challenge posed by Microsoft to Apple.
The Microsoft Surface saw its official release on 19th June in the city of Los Angeles. It has made a great first impression and seems to be beginning a new start in the competition between the best tablets in the international market. It has 10.6’’ screen and a magnetic cover that can be used as a keyboard and also as a kickstand in order to place the device upright on tables. There has been a paradigm shift in Microsoft’s policy when it decided to do away with the tile-based Metro theme for its Desktop that is almost a trademark with it.
There are many features that make the Surface more like a laptop than like a tablet- the most prominent one being the built- in keyboard that will be useful for business customers. As Microsoft Surface employs Windows 8 as an operating system, which is also used in its computers and laptops, it will be a lot easier for customers to switch among their devices.
The tablet was announced by Microsoft’s CEO, Steve Ballmer, in Los Angeles at a special press conference. It was hailed to be the first of an entirely new family of a number of devices being created and developed by the company. The Surface has a thickness of 9.3mm and weighs 1.5 pounds. It has a kickstand and keyboard for its cover. It is 0.1 mm thinner than the iPad 3, which is the latest iPad from Apple.
Getting involved with the IT, or Internet Technology industry, is a way for you to break into a variety of potential coveted career paths and job openings. Whether you prefer working with the back-end of programming or if you enjoy improve user experience while browsing online, there are many different in-demand IT skills that are useful to obtain today if you are seeking a career in the tech industry yourself.
Cloud Computing
Working with cloud computing, otherwise known as "the cloud", requires you to work within various types of servers that store and access data globally from any location. With the increase in mobile usage, cloud computing is becoming even more prevalent in today's society. When you want to work with cloud computing, understanding the basics of programming and network security is a must. Working in cloud computing is a way to help with building new applications, expanding companies online as well as allowing anyone internationally to locate and access a specific blog, website or mobile app.
UX Design
UX Design is also known as user experience design. A user experience designer specializes in understanding the usability and overall experience a web visitor has when browsing on a site or blog. UX design is essential to ensure that all visitors on a website are capable of navigating the blog properly and accessing the site's content with ease, regardless of the browser they are using or the type of device that is being used to access the site itself. Cross-browser compatibility and ensuring that all websites you are working with are accessible via mobile platforms is another responsibility of many UX designers today. Working in UX design is highly recommended if you believe you have an eye for "good" web design and if you have an interest in improving the overall experience web users for a specific audience have when visiting the blog or website you represent or that you are building for yourself.
IT Security
IT security is one of the fastest-growing positions throughout the entire IT industry and field. IT security requires you to understand network infrastructures as well as how to properly manage each server individually to provide security and protection from potential hackers and online thieves looking to steal sensitive data and information. Maintaining the security of a network and all servers for a company is only becoming more popular with the expansion of mobile phone usage along with the growth of the Internet altogether.
Understanding the variety of IT skills that are in demand today can help you to better decide on a path that is right for you. The more you understand about various IT skills, the easier it is to find a position or career in your future that is most suitable for the type of work you enjoy. Whether you are looking to develop new apps or if you are interested in managing the security of company servers, there are hundreds of positions and skills that are in demand in the IT industry today.
What are the best languages for getting into functional programming?
One of the biggest challenges in pursuing a career in software development is to figure out which language you want to work. In addition to commonly used software programming languages like C, C++, Java a lot of new programming languages such as Python, Ruby on Rails have surfaced especially because they are used by a lot of consumer based start-ups these days.
With so many front and back end languages, the choice of learning Java is a failsafe decision and mastering Java can ensure that you have a bright future in software programming.
What is Java
Java is a computer programming language that is designed to be platform independent meaning that the language can virtually run on any hardware platform. This platform independence and an object oriented framework make Java the preferred language of development especially for client-server web applications.
Tech Life in Arkansas
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Murphy Oil Corporation | El Dorado | Energy and Utilities | Gasoline and Oil Refineries |
| J.B. Hunt Transport Services, Incorporated | Lowell | Transportation and Storage | Freight Hauling (Rail and Truck) |
| Tyson Foods, Inc. | Springdale | Manufacturing | Food and Dairy Product Manufacturing and Packaging |
| Dillard's, Inc. | Little Rock | Retail | Department Stores |
| Wal-Mart Stores, Inc | Bentonville | Retail | Department Stores |
| Windstream Corporation | Little Rock | Telecommunications | Telephone Service Providers and Carriers |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Arkansas since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Linux Unix programming
- Get your questions answered by easy to follow, organized Linux Unix experts
- Get up to speed with vital Linux Unix programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…

